The latest version (8.2.x) of Tivoli Endpoint Manager comes with it the ability to authenticate console users with your LDAP directory. Here is a simplified step-by-step guide for setting that up.
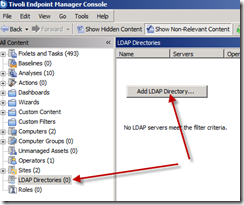
Open your console and use one of your Master Operator accounts. Find the LDAP Directories branch in the left side tree and right click it. Choose to Add LDAP Directory from that list…
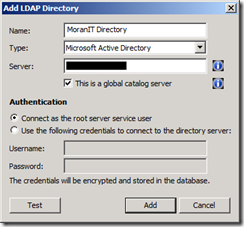
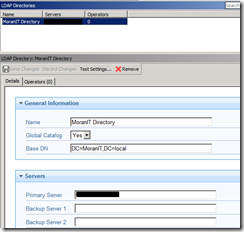
Enter any “Name” you’d like and specify your LDAP authentication server as well as if it is a global catalog server. In my tiny network, I only have the one DC.
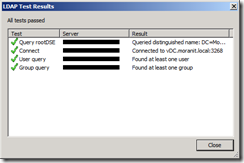
Click the Test button to validate the connectivity…
My network is very tiny, however I would encourage you if alternate DC servers are available to specify them in the Backup Server X spaces provided.
Adding the link to the DC is one step… next you’ll probably want to create a special AD group which Console users will belong. Remember that within TEM, we have Console Operators and Master Operators. Each user/group has a specified set of computers they are responsible for and this can be extended into AD. Simply create a AD user group for how your organization is divided and based on their required level of console access.
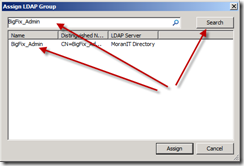
In my case I created two AD groups: BigFix_Admin and BigFix_Console. Then added my user account to the Admin group.
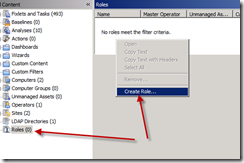
Our next/last step is to specify the level of access each of these new AD groups have within the TEM infrastructure.
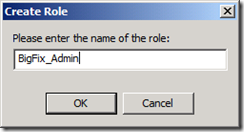
You can name this new Role anything you’d like, however I like to match the AD group name up with this Role name to make it easy to understand.
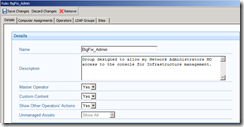
My Admin group has near unlimited privileges… thus I’ll chose yes to the following options: Master Operator, Custom Content, and Show Other Operators’ Actions.
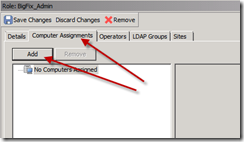
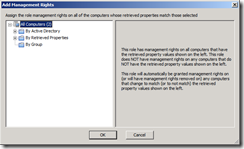
Next we’ll need to assign the computers that this group will have control over… in my case I’ll be specifying “all computers”
Using this dialog I can specify individual computers as well as systems based on Retrieved Properties or Group Membership.
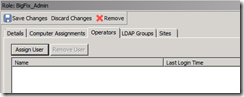
I will not be adding TEM users to this group as it was setup specifically for my LDAP Admin group… so I’ll skip the “Operators” tab.
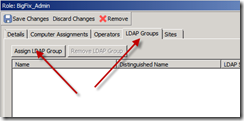
Instead I’ll be focusing on the LDAP Groups tab… and Assigning LDAP Group to this TEM Group I’m currently defining…
Search for the group to be added to this TEM group, and Assign it.
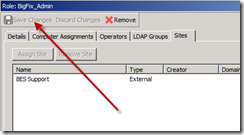
Lastly I’ll glaze over the Sites tab since I currently only have 1 site in this new infrastructure, however I can specify specific site permissions just like I can for TEM users.
Don’t forget when you are done to Save Changes…
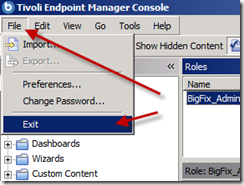
Since this is a fresh installation, the setting which requires entering your authentication password to authorize this new action has been disabled by default. In a different article I will explain this very cool security feature, how it works and how to force the password requirement just like in previous versions. For now, let’s log in with my Domain credentials to test things out!
Let’s re-launch the console but this time using my Domain credentials…
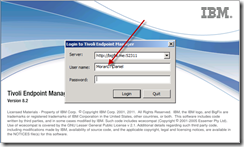
Be sure to include your Domain within the User name field… In my case it’s “MoranIT\Daniel”
Success!! The authentication was accepted and I’m logging into the console!
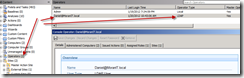
Something very important to notice here is that my operator site and account was automatically generated upon login. This means that if too many new users login it could cause network traffic on your network since a subscription action is deployed to the authorized computers list.
Enjoy your new LDAP authenticated user access… let me know if you have any questions or comments in the section below. I respond to all my comments, so please engage…




I’ve been using Tivoli with LDAP authentication for some time. I’ve created lots of LDAP Operator accounts in the console. Recently one of the sites requested that they be able to add LDAP Groups. I created corresponding Roles in Tivoli, and then added the LDAP groups to the Roles.
However, if an Operator had previously been using an LDAP Operator account, and their account appears in one of the newly added LDAP groups, then they receive an error when they try to connect. The error message states that the Operator account already exists.
Have you seen this? I would suspect my solution is to remove any LDAP Operator accounts that might be included in the newly added LDAP groups.